Flash USDT Is a Scam Developers Still Get Asked to Build

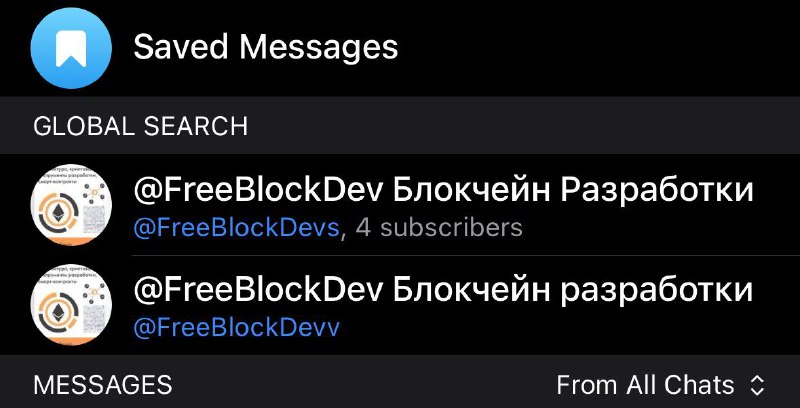
Over the past year, I’ve had people message me more than 10 times asking for development help with a “Flash USDT smart contract.” The messages are usually polite. Sometimes they even come with a technical spec, as if it’s a legitimate Web3 product request.
It isn’t.
“Flash USDT” is a recurring scam theme—fraud disguised as smart contract development. I want to break down the mechanics so developers don’t get pulled into building it, and users don’t get tricked by the “transaction proof” it produces.
What “Flash USDT” is supposed to be (and what it really is)
In these pitches, scammers describe a token or contract that can “send USDT” without actually transferring funds. The promise is always some variation of:
- “It will show up in MetaMask / on the explorer as received USDT.”
- “It’s just a fast arbitrage / liquidity contract.”
- “We’re not stealing—just simulating a transfer.”
In reality, the goal is to create a visual imitation of a USDT transfer—something that looks convincing to a non-technical person at a glance, but is not a real USDT transfer.
How the Flash USDT scam typically works
1) They try to recruit a developer
The first move is to approach Solidity developers and ask them to build a contract that “works with liquidity” or “executes quick arbitrage.” The actual request, once you read between the lines, is simple: make it look like USDT was sent without affecting the real USDT balance.
This is a huge red flag. Legitimate contracts don’t “simulate” transfers of someone else’s token balance. USDT transfers are governed by the official USDT contract—if you didn’t call transfer (and it didn’t succeed), you didn’t transfer USDT.
2) They generate a fake-looking “transaction”
The scam contract is then used to produce something the attacker can show to a victim—often a transaction hash, a UI display inside a wallet, or activity that looks like a transfer on a block explorer.
The key detail: it’s not a real USDT movement. It’s a trick built on how interfaces display token activity and how easy it is to confuse “a transaction happened” with “funds were actually transferred.”
3) They use it to persuade a victim to send real money
With the fake “proof” in hand, the scammer approaches a target. Common contexts include:
- Buying an asset OTC (“I already sent you USDT—look, here’s the transaction”).
- Showing “investment profit” (“Your balance increased—now send a withdrawal fee / top up”).
- Any peer-to-peer deal where someone can be pressured to act quickly.
The victim sees something that resembles a USDT transfer and, without verifying the token contract and actual balance change, sends real USDT (or other assets) in return.
4) The scammer disappears
Once the victim sends actual funds, the attacker vanishes. There’s no dispute resolution in a scam, and on-chain finality doesn’t care about screenshots.
Why this matters (for developers and for users)
If you’re a developer
Don’t take these “Flash USDT” requests. It’s not a clever DeFi mechanism—it’s direct participation in a fraud scheme. The fact that the request is wrapped in polite language or a “technical specification” doesn’t change the intent.
If a client asks you to build anything that:
- “Makes transfers appear” without real token movement,
- “Shows funds received” without using the official token contract,
- or relies on confusing a counterparty during a trade,
…you’re looking at a scam pattern, not a product.
If you’re an investor or everyday user
Be skeptical of any “payment proof” that’s based on interface visuals. Verify:
- That the token contract address is the real USDT contract for that chain.
- That your balance actually increased.
- That the explorer entry corresponds to a successful token transfer event from the official contract (not just any transaction).
If someone shows you a “transfer” but it doesn’t reconcile cleanly with your actual balance and the official token contract, treat it as an attempted scam.
Final note
Web3 is full of legitimate innovation—and also repeatable fraud templates. “Flash USDT” is one of those templates. The best defense is basic verification, and the best way to starve these schemes is for developers to refuse to build them.

Alex Meleshko
Entrepreneur, CEO, and builder at the intersection of blockchain, AI, and startups.