Upwork Scams Targeting Blockchain Developers: What I Learned While Landing My First Job
Recently I started actively building up my Upwork profile to find new clients for blockchain development. Getting the first real contract is predictably hard—not only because of competition, the “crypto winter,” or the usual new-profile friction, but also because you end up spending a surprising amount of time on fake job posts.
And it’s not just time. You also burn Connects—a paid resource, very much in line with the capitalist nature of the platform. Without Connects you can’t pitch yourself, and the more loudly you want to pitch, the more Connects you’ll spend. Losing them to scams is frustrating.
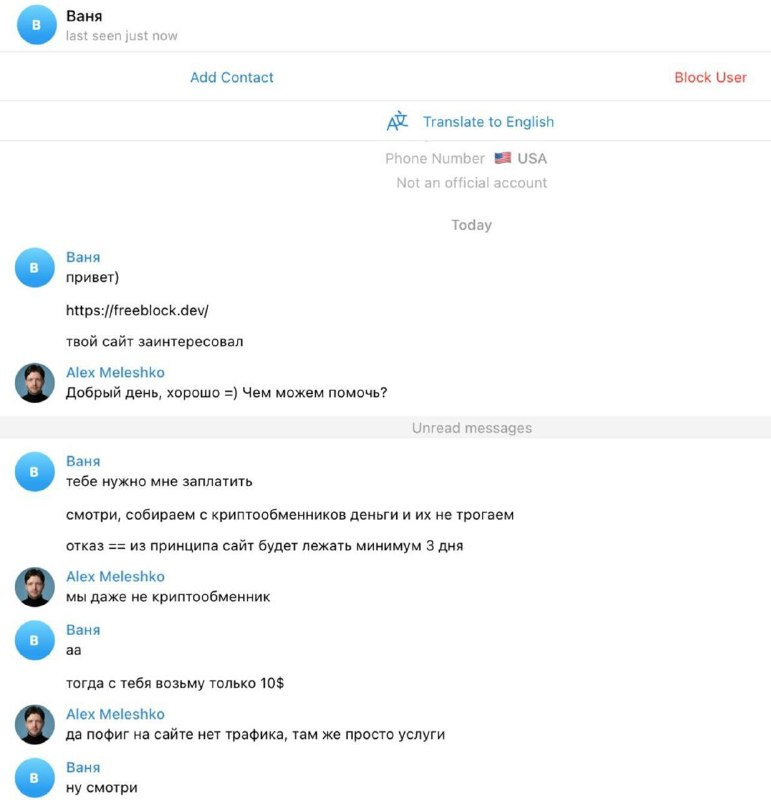
What the scam is really about
The core of the scheme is simple: the “client” tries to get you to deploy something locally—a project repo, an archive, a “test assignment,” or a “codebase for review.” The goal isn’t your engineering opinion. The goal is to get malware onto your machine.
Typical framing looks like this:
- “Can you run this project locally to review the architecture?”
- “Prove you’re not a scammer—deploy it on your machine and send a screenshot.”
- “Before we start, check this code quickly; it’s just for familiarization.”
In other words: they’re hunting for a Web3 developer, hoping for access to something valuable—accounts, wallets, credentials, repositories, client data—anything. Some of them are surprisingly persistent and polished.
Red flags I’ve learned to watch for
Not every new account is malicious, but a combination of the signals below is usually a good reason to step back and validate carefully:
- Very fresh profile.
- Instant response to your proposal, overly friendly, and agrees with everything you suggest.
- No reviews.
- No paid contracts (or no visible hiring history).
- Unverified payment method. (Even verified payment isn’t a guarantee—I’ve seen suspicious cases there too.)
- Template-like project description: vague scope, few details, shallow answers. Some scammers do the opposite—overprepare and flood you with “requirements” to look legitimate.
- Promises unusually high pay while showing little interest in your actual competence or process.
- “Fancy” GitHub account that looks curated but is new and lacks real signals (history, badges, long-term activity).
How I handle it now
I don’t run random code from strangers on my main machine. If I absolutely must evaluate a repo, I do it with strict isolation (and only after confirming the client is real):
- Ask clarifying questions about the product, users, and success criteria. Scammers usually collapse under specifics.
- Request a proper Upwork contract setup before any “tests.”
- Never download executables or “installers” as part of a test task.
- If review is necessary, use a disposable environment (separate VM/container) and treat it as untrusted.
Most importantly: trust your instincts. If the conversation feels off, it usually is.
Why this matters beyond Upwork
We get plenty of inbound requests from regular users asking for help recovering lost funds. The more popular crypto becomes, the more victims there are—across all kinds of schemes. Freelancers and developers are a particularly attractive target because we have access to systems, credentials, and sometimes wallets.
Take care of yourselves and stay alert.
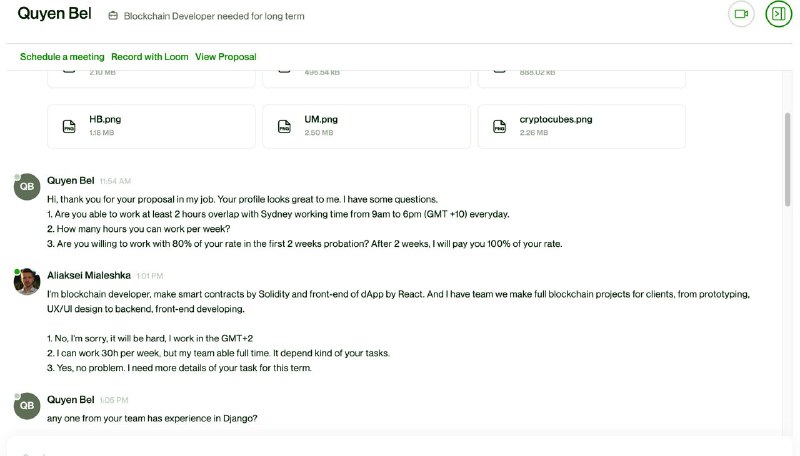
P.S. The good news: I did land my first Upwork job—and got 5 stars.

Alex Meleshko
Entrepreneur, CEO, and builder at the intersection of blockchain, AI, and startups.